Introduction
The security requirements for 802.11 wireless networks that are used to receive, store, process and transmit federal tax information (FTI), and provides agencies best practices for designing a Publication 1075, Tax Information Security Guidelines for Federal, State, and Local Agencies (Pub. 1075), compliant wireless network.
This includes wireless networks located at the agency’s office or data center where FTI is received, stored, processed or transmitted from; however, this memo does not cover the use of public or personal Wi-Fi networks for remote access to FTI through publicly available or personally owned wireless networks.
As agencies look for ways to reduce their infrastructure costs, wireless implementations are becoming more common, making these protocols imperative. A wireless environment usually takes place in one of two scenarios:
- A user connects to a local area network (LAN) without physically connecting their device(s) through a wired Ethernet connection. Wired LANs utilize physical cables and circuits that are contained within a specific location.
- A wireless local area network (WLAN) uses radio waves to broadcast network connectivity to anyone who is within a limited receiving range, such as an office building. WLANs are usually implemented as extensions to existing wired LANs utilizing wireless switches or access points (APs) to deliver connectivity to wireless clients such as laptops or mobile devices. a WLAN uses radio waves that propagate in the air through physical boundaries such as a floor or building, extending the boundary of the LAN and potentially increasing the risk of the data being exposed to eavesdropping by an unauthorized user.
Because of the broadcast and radio nature of wireless technology, ensuring confidentiality and authentication is significantly more difficult in a wireless network than a wired network. WLANs are typically considered less secure than a wired LAN due to weak security configurations that favor convenience of access over security.
In addition to being susceptible to the same threats as the wired LAN, data transmitted via a WLAN is also susceptible to eavesdropping and interception through the air by an attacker within range of the wireless transmission, wherein the attacker passively monitors network communications for data, including authentication credentials.
In addition to eavesdropping, another common threat against wireless networks is the deployment of rogue wireless devices for masquerading or man-in-the-middle attacks. An attacker could deploy a wireless AP that has been configured to appear as part of an agency’s wireless network infrastructure, which would circumvent perimeter security controls, provide the attacker a backdoor into the wired network and allow the attacker to actively impersonate a legitimate AP and accept client connections.
Managing WLAN security is a complex and dynamic task that poses new challenges to network and security administrators. Agencies contemplating using FTI in a WLAN deployment can mitigate many of the WLAN security risks by developing a security policy with a strong set of security requirements that must be satisfied before deployment.
Wireless components and architecture
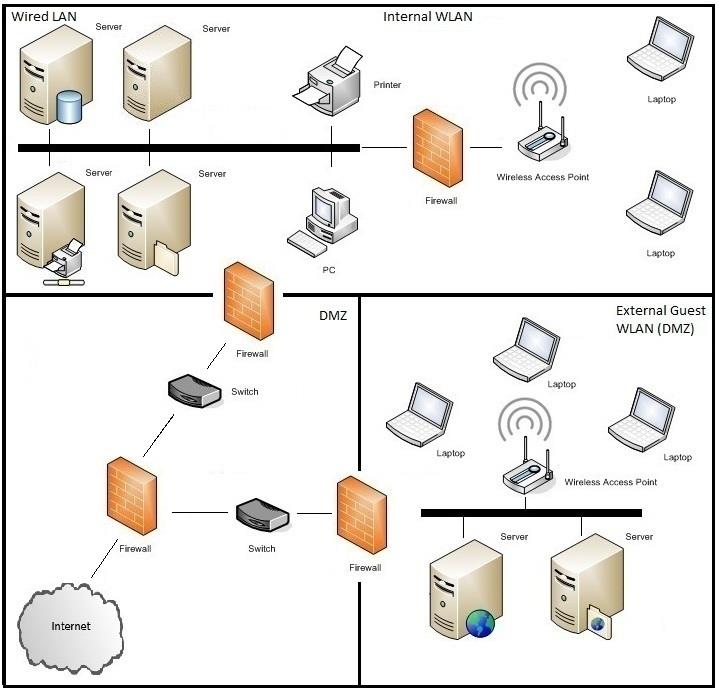
The security of a WLAN is heavily dependent on how well each WLAN component is secured throughout its lifecycle. A WLAN deployment typically consists of these components: Access Points, Client Devices, Firewalls and Wireless Switches. Any external facing Access Tier components such as web servers and interface servers must be placed behind filtering devices in a Demilitarized Zone (DMZ).
- Access Point is a device that logically connects client devices with the wired network using radio waves or other wireless protocols based on the IEEE 802.11 standard.
- Client Devices are devices that communicate with access points through Wi-Fi. These devices include, but are not limited to, lap top computers, mobile devices and PC Cards.
- Wireless Switch is a device that logically connects the access points to the wired network. Through this device an administrator can manage and control all wireless network functions from a central point.
- Firewalls provide separation between wireless and wired networks as well as fine-grained security within a wireless network.
Figure 1. WLAN Components and Architecture
Mandatory Requirements for FTI in a Wireless Environment
To utilize FTI in an 802.11 WLAN, the agency must meet the following mandatory requirements:
- The agency should have WLAN management controls that include security policies and procedures, a complete inventory of all wireless network components and standardized security configurations for all components.
- WLAN hardware (access points, servers, routers, switches, firewalls, repeaters) must be physically protected according to the minimum protection standards for physical security outlined in Pub. 1075, section 2.B, Secure Storage.
- Each system within the agency’s network that transmits FTI through the WLAN must be hardened in according to the requirements of Pub. 1075.
- The WLAN is architected to provide logical separation between WLANs with different security profiles, and from the wired LAN.
- WLAN infrastructure that receives stores, processes or transmits FTI must comply with the IEEE 802.11i wireless security standard and perform mutual authentication for all access to FTI via 802.1X and Extensible Authentication Protocol (EAP).
- Vulnerability scanning must be conducted as part of periodic technical security assessments for the organization’s WLAN.
- Wireless intrusion detection is deployed to monitor for unauthorized access, and security event logging is enabled on WLAN components according to Pub. 1075, Exhibit 9.
- Disposal of all WLAN hardware follows media sanitization and disposal procedures from Pub. 1075.
These requirements are explained in detail in the sections below.
1) WLAN Management Controls
The WLAN management controls fall into the categories of policy and procedures, device inventory and baseline configurations.
Policy and procedures
Developing strong security policies and procedures is the first step in ensuring protection of FTI in a wireless network. Policy and procedure must cover management and monitoring of the WLAN, including topics such as training, acceptable use, encryption, passwords, identity, client device security and privacy. Agencies must have policies that clearly state which forms of connections are permitted or prohibited for their WLAN client devices under various circumstances. Agencies must enforce these policies through the appropriate security controls.
These guidelines must provide a complete inventory of all wireless system components such as access points, wireless switches, client devices and any other equipment within your WLAN. The inventory must be updated on a periodic basis, at a minimum annually, to account for device changes.
Agencies must have standardized security configurations for their common WLAN components, such as client devices and APs to ensure a standard level of security is implemented while reducing vulnerabilities and lessening the impact of successful attacks. These configurations must be deployed to the appropriate devices, and maintained throughout their lifecycle. If implemented correctly standardized configurations can significantly reduce the time and effort needed to detect and correct unauthorized changes to configurations, and to react quickly when newly identified vulnerabilities arise.
2) Physical Protection of WLAN Hardware Components
Unless the WLAN is encrypted, anyone with physical access to it could potentially connect network monitoring tools and tap into the WLAN. Therefore, agencies must ensure that adequate physical security is in place to restrict access to WLAN components, which includes access points, servers, routers, switches and firewalls.
Pub. 1075 requires two barriers to access FTI under normal security, i.e., a locked perimeter and secured interior area. Locked means an area that has a lock with controlled access to the keys or combinations. Secured interior area refers to internal areas that have been designed to prevent undetected entry by unauthorized persons during duty and non-duty hours. Non-agency personnel may not reside in computer rooms and/or areas containing FTI unless the person is authorized to access that FTI.
Secured perimeter/secured area must meet the following minimum standards:
- This area must be enclosed by slab-to-slab walls constructed of approved materials and supplemented by periodic inspection or other approved protection methods, or any lesser type partition supplemented by UL-approved electronic intrusion detection and fire detection systems.
- Unless electronic intrusion detection devices are used, all doors entering the space must be locked and strict key or combination control must be exercised.
- The space must be cleaned during duty hours in the presence of a regularly assigned employee.
- There must be at least two barriers (combination of physical and electronic) between the equipment which handles FTI in the WLAN environment, and those who are not authorized to access FTI.
3) WLAN System Component Hardening
Each system component within the agency’s network that transmits FTI to an external customer through the use of WLAN must be hardened in accordance with Pub. 1075. This includes access points, client devices, switches and firewalls.
All platforms supporting the WLAN must be hardened to Pub. 1075 standards by utilizing the Safeguards Computer Security Evaluation Matrix (SCSEM). These SCSEMs are available for download from the IRS Safeguards web site. A vendor neutral, WLAN-specific SCSEM is also included in this library, but agencies are encouraged to review all SCSEMs to achieve overall compliance for the components that comprise the WLAN.
Client devices
Client device security is an important piece in the overall protection of the agency’s WLAN and FTI. Client device security controls include using personal firewalls, host-based intrusion detection and prevention systems and antivirus software on client devices; disabling IEEE 802.11 ad hoc mode; managing IEEE 802.11 radios, such as disabling them when not in use and configuring client devices to comply with WLAN policies. Client devices must also be kept current with patches and updates.
Agencies must implement the following controls to secure client devices:
- All client devices accessing the WLAN must have anti-virus software installed and updated with the latest virus definitions and a host-based firewall or intrusion detection system to prevent viruses and other malicious content from infecting the agency network.
- Client devices must be configured so that they do not automatically connect to WLANs. If this configuration is not set, client devices inadvertently may connect to rogue access points exposing the device to malicious attacks. In addition, if the user has no business need to connect to the agency’s network through wireless means, then they must have their wireless radios disabled by default. Users must disable their wireless radios when not in use.
- If a client has IEEE 802.11 ad hoc mode enabled, it must be disabled if unneeded and feasible. With this mode enabled other users may be able to inadvertently or maliciously connect to the client device.
- Personal firewall software must be installed and configured to block unauthorized access on all mobile and employee-owned computers that are used to connect to the agency's network and to the Internet. Personal firewalls increase device security by offering some protection against malware that may through vulnerable ports and openings on your device.
Access points
There are two types of wireless access points called thick (intelligent) and thin. Thick APs handle authentication and encryption as well as overall management of the network clients, whereas thin APs have limited intelligence and are managed by a centralized WLAN controller. Thin APs are generally more secure than thick APs because thin APs do not have a key that could be extracted and do not require the same level of physical security and other countermeasures than thick APs.
Agencies must implement the following controls to secure access points:
- The AP’s default settings must be changed to reflect the agency’s security policy, such as changing the default service set identifier (SSID) and requiring the use of a strong administrator password that meets Pub. 1075 requirements. In addition, the AP must employ a timeout threshold of 15 minutes of inactivity to require re-authentication and must lock out after three failed logon attempts. Administrator access to the AP must be limited to only authorized administrators. The SSID must not reflect or easily identify the agency.
- The APs reset functionality must be managed to prevent any unauthorized access to the agency’s network. A malicious user could utilize the reset function to restore all settings to their default factory values, thereby circumventing any security measures set by the administrator. The agency must have policies in place to limit the use of the reset function and restrict it to authorized personnel.
- All non-essential and insecure management protocols of APs must be disabled.
- A non-essential protocol is one that is not required for normal business operations.
- Insecure protocols include, but are not limited to, Simple Network Management Protocol (SNMP), Telnet, and File Transfer Protocol (FTP). APs that support Simple Network Management Protocol (SNMP) protocol must be configured for least privilege (i.e., read only). If SNMP is not required for the WLAN, it must be disabled; otherwise, SNMPv3, which includes mechanisms to provide strong security, is required over SNMPv1 and SNMPv2 because those versions support trivial authentication based on plaintext community strings and are fundamentally insecure. If an unauthorized user were to gain access and had read/write privileges, that user could write data to the AP, compromising its original configuration.
- A non-essential protocol is one that is not required for normal business operations.
- Utilize media access control (MAC) address filtering to control the wireless clients’ access to the network through an access control list (ACL). When enabled, the ACL identifies clients by their MAC addresses and restricts access to only devices with addresses that are in the list. Devices with MAC addresses not in the list will fail to associate to the WLAN. However, device MAC addresses can be easily changed and spoofed, and they are transmitted in the clear leaving them exposed to packet sniffing and giving a hacker the ability to impersonate a valid client device and gain access to the network. The administrative overhead of managing MAC ACLs may also be burdensome in medium to large WLANs. Therefore, MAC ACL filtering does not represent a strong security control by itself, but adds an additional layer of defense to the agency’s security posture.
4) WLAN Architecture
An agency should utilize Layer 2 switches in their WLAN network architecture as an alternative to Ethernet hubs. A hub is a device that physically connects all stations on a local subnet to one circuit, but maintains no knowledge of what devices are connected to its ports. Ethernet hubs broadcast network traffic to all physical interfaces and connected devices, which leaves the broadcasted traffic vulnerable to unauthorized monitoring. The use of the Ethernet hub infrastructure increases the risk that the AP may be broadcasting FTI that was transmitted through the hub. Switches alleviate this concern by providing dedicated channels between communication devices.
Layer 2 switching is hardware-based switching using the media access control address (MAC address) from the host's network interface cards (NICs) to decide where to forward frames. Advantages of switches are that a switch can manage a larger total volume of data in transit at any given time, use MAC address and can support VLAN's that can help in logical segmentation of ports.
Network separation
A WLAN is usually connected to an organization’s wired networks as an extension to the wired network to allow mobility for network access. WLANs may also be connected to each other. An important security control for WLAN security is to logically separate the WLAN from the wired LAN and separate WLANs with different security profiles. This is most commonly done by installing a firewall between the WLAN and the wired networks to enforce a security policy on the information flows.
WLANs for external (guest, etc.) and internal use must be separated and devices on an agency’s external WLAN must not be able to connect through that WLAN to devices on another of the organization’s WLANs. WLANs that are used to provide guest Internet access must be architected so that their traffic does not traverse the agency’s internal networks. The guest WLAN must be logically separated from the employee WLAN using network firewalls in a DMZ. Client devices on the external or guest WLAN must only be allowed access to the necessary hosts or subnets using only the required protocols, and must be denied access to the internal network and FTI.
Dual connecting
In addition, client devices must not be allowed to “dual connect”, where a client device is connected to a WLAN and the agency’s wired LAN concurrently, without a valid business need and a policy that clearly states the forms of dual connections that are permitted and prohibited.
The primary concern with dual connected configuration is that an attacker may be able to gain unauthorized wireless access to the client device and then use it to attack resources on the wired network, allowing the attacker to exploit the lower-security network to gain access to the higher-security network.
It also violates the principle of disabling unneeded services to reduce attack surface; if the device is already connected to a wired network access, an additional connection to the WLAN is not necessary.
Management traffic
Agencies must also ensure that the confidentiality and integrity of their WLAN management traffic is maintained. This can be done through use of Virtual Private Networks (VPNs) and placing the traffic on a dedicated wired network or a virtual local area network (VLAN), in addition to using Secure Socket Layer/Transport Layer Security (SSL/TLS) for web-based management of wireless access points.
5) WLAN Infrastructure
All connections to WLANs that receive, store, process or transmit FTI must use the IEEE 802.11i Robust Security Network (RSN) framework with IEEE 802.1X and the Extensible Authentication Protocol (EAP) authentication to establish a secure wireless connection between WLAN devices. The 802.1X standard provides for port-based authentication, ensuring a client device is authenticated prior to gaining WLAN access.
Standards previous to IEEE 802.11i used authentication methods such as Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA), which have known security flaws and vulnerabilities, been proven insecure and therefore cannot be considered a secure standard.
WEP is vulnerable due to the manner in which it implements the RC4 stream cipher algorithm. WLANs using WEP are vulnerable to eavesdropping and unauthorized access. WPA improved upon WEP by securely implanting RC4; however, it does not provide support for the Advanced Encryption Standard (AES). WLANs that receive, process, store or transmit FTI cannot use WEP or WPA as the security standard.
WEP and WPA have been replaced by several standards, WPA2 and the IEEE standards, 802.11i and 802.1X. WPA2 does implement the majority of the IEEE 802.11i standard, but it is not an IEEE standard, and not fully compatible with the standard.
Agencies using legacy IEEE 802.11 WLAN security standards or pre-shared keys (PSK) should upgrade to an enhanced standard such as 802.11i method with IEEE 802.1X / EAP that provides security features to protect FTI. PSKs should be avoided since these keys are derived from a passphrase shorter than approximately 20 characters. This provides relatively low levels of security and may make the environment prone to dictionary and rainbow attacks.
For FTI transmission, the WLAN infrastructure must comply with IEEE 802.11i and use WPA2 certified devices with the following settings implemented:
- AES encryption with a 256-bit key,
- CCMP (Cipher Block Chaining Message Authentication Code Protocol) used to handle both packet authentication and encryption,
- The pairwise master key (PMK) must have a lifetime of 24 hours or less and
- The group master key (GMK) must have a lifetime of 8 hours or less.
A fallback method for failed wireless authentication (e.g., forgotten passwords and lost smart cards) shall be at least as strong as the primary method.
6) Security Assessments
Comprehensive WLAN security assessments must be conducted at least annually to understand WLAN threats, the likelihood that those threats will be realized and the potential impact of realized threats. This allows weaknesses to be identified before they can be exploited and to ensure that the agency’s implemented security measures are working as intended.
6.1) Vulnerability Assessment
Vulnerability scanning and assessments can be performed for WLAN components. Many modern vulnerability scanners have the ability to login to Cisco wireless devices and determine if they are running the latest firmware and patch levels. The vulnerabilities identified during periodic security assessments must be documented in a plan of action and milestones (POA&M), and mitigation actions tracked to completion.
6.2) Physical & Logical Site Survey
The assessments should include a review of all AP locations and an assessment of the AP range to determine the coverage area and to ensure that communications do not extend beyond the agency’s documented boundaries. Assessors, such as security administrators or auditors, can use sniffers to determine whether wireless products are transmitting correctly and on the correct channels. Assessors should periodically check within the office building space (and campus) for rogue APs and other unauthorized access. The vulnerabilities identified during periodic security assessments should be documented in a plan of action and milestones (POA&M), and mitigation actions should be tracked to completion.
7) Monitoring and Logging
In addition, agencies must implement wireless intrusion detection and prevention services to detect unauthorized, "rogue" access points and other wireless threats that may expose FTI. WIDS agents shall be deployed in the 802.11 WLAN where FTI is transmitted and accessed to detect suspicious behavior and unauthorized wireless access or activity.
The WIDS must detect and log the following minimum events:
- Unauthorized radio transmitters,
- Unauthorized clients attempting to associate with an access point that transmits FTI,
- Authorized devices communicating with unauthorized devices and
- Denial of service attacks (DoS) and interference.
All WLAN components, including client devices, access points, switches and firewalls that connect to a wireless technology or device, must ensure compliance with audit logging standards found in Pub. 1075, enable logging on APs to ensure user accountability and provide records that can be reviewed if malicious activity has occurred to better understand the nature of that activity.
The agency must regularly review the system logs to ensure that they are continuously monitoring their WLANs for both WLAN-specific and general (wired network) attacks.
8) Disposal
When disposing of a WLAN component, the agency must remove all sensitive configuration information, including pre-shared keys and passwords in accordance with the sanitization requirements described in Pub. 1075. In addition, the agency must ensure that its audit records are retained as needed to meet legal or other requirements.
Resources
- Publication 1075, Tax Information Security Guidelines for Federal, State and Local Agencies
- NIST SP 800-153, Revision 4, Guidelines for Securing Wireless Local Area Networks (WLANs) PDF
- NIST SP 800-48, Revision 1, Guide to Securing Legacy IEEE 802.11 Wireless Networks PDF

 )
or https:// means you've safely connected to the .gov website. Share sensitive information only on official, secure websites.
)
or https:// means you've safely connected to the .gov website. Share sensitive information only on official, secure websites.