Introduction
Virtual desktop technologies enable the hosting of a desktop operating system within a virtual machine (VM) running on a centralized server. A virtual desktop infrastructure (VDI) provides users access to enterprise resources, including a virtual desktop from locations both internal to and external to the agency’s networks.
Per Publication 1075 Section 3.3.7 Virtual Desktop Infrastructure authorized users can access federal tax information (FTI) by connecting to their virtual workstation via a vendor specific agent, connection client or through an Internet browser from practically any mobile device with Internet access. This can offer significant savings to agencies from a cost and management perspective, allowing agencies to largely centralize patch management and deploy standardized desktop configurations.
Numerous vendors offer a variety of VDI solutions, each agency should carefully select the desktop virtualization solution that best fits to their operational environment and end user needs, while ensuring security of FTI received, stored, processed, or transmitted in a virtual desktop environment. See Publication 1075 Section 4.1 Access Control (AC-20) Use of External Systems for additional information.
Virtual desktop components and architecture
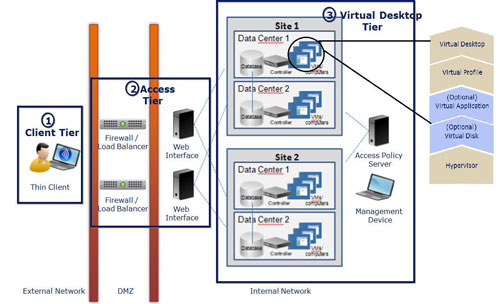
A typical virtual desktop deployment consists of four tiers:
- Tier 1: Client - includes thin client devices, like laptops and desktops, which end users employ to access their desktop within the virtual desktop tier.
- Tier 2: Access - consists of entry points to the virtual environment. Access Tier devices include gateways, web interfaces, authentication servers and session managers. This tier brokers connections between Client Tier devices and Virtual Desktop Tier components.
- Tier 3: Virtual Desktop - contains virtual desktop images residing on servers in the data center. Other components within the Virtual Desktop Tier include management consoles, databases, virtualization components that publish virtualization resources and a hypervisor that handles execution of the virtual environment. A virtual desktop is built using a modular approach where each component layers on top of another component to give the end-user a customized desktop environment.
- Tier 4: Client Application - includes the applications that are delivered to the end user via the virtual desktop. This tier will not be addressed in this memo as it is application level.
Figure 1 - Virtual Desktop Components and Architecture 1
Security challenges to virtual desktop
Virtual Desktops allow users to remotely access their desktop from a variety of locations. The following risks are unique to a virtual desktop environment and can jeopardize the confidentiality, integrity and availability of FTI if protection is inadequate:
- Client Tier devices can be operated from a remote location, such as a public space, where physical security controls are inadequate.
- Sensitive information traverses over networks where the agency cannot control security.
- Users can potentially store FTI locally on the thin client or removable media by escaping the confinement of the virtual desktop using guest-to-host operations. FTI can also be printed locally if the virtual environment is not securely configured.
- Virtual desktops are prone to virtualization specific attacks, such as hyperjacking, in addition to the traditional threats such as viruses, Trojans, man-in-the-middle attacks, key loggers, root kits and client-side attacks that are targeted against Client Tier devices.
- Security event auditing is more complex and cumbersome in the virtual environment. Log correlation can be difficult to accomplish leading to undetected security incidents.
- Internal resources that were not previously accessible from external networks are vulnerable to new threats from untrusted client device.
Mandatory requirements for FTI in a virtual desktop environment
To utilize Virtual Desktop that provides FTI to a customer, the agency must meet the following mandatory requirements to lower the residual risk of the potential weaknesses identified in the section above:
- Environment segregation: Virtual Desktop components must be segregated so boundary protections are implemented and access controls are granulized.
- Access control: An access control system must be specifically configured to address the complicated nature of the environment, ensuring only authorized clients that conform to agency security policy are permitted access to the VDI.
- Securely configure components within the Virtual Desktop and Access Tiers: Configure the hypervisor, management consoles and other virtual desktop components using secure configuration guidelines provided by the vendor.
- Managing user privileges: The least privilege principle must be strictly enforced in a virtualized environment.
- Limit functionality provided by the virtual desktop: Configure the virtualized desktop to provide only the functionalities required for operations. Non-essential functionality or components must be removed or prohibited. See Publication 1075 Section 4.5 Configuration Management (CM-7) Least Functionality for additional information.
- Multi-factor authentication: Users authorized to access FTI must use multi-factor authentication to validate their identity.
- Audit privileged and administrative functions: All privileged and administrative functions must be recorded by the system. (See heading below for additional guidance).
- Session confidentiality and integrity: FTI must be transmitted securely using end-to-end encryption.
Environment segregation
- Major VDI components such as databases, application servers and management software must be installed on dedicated platforms to prevent unauthorized access.
- If a design validation farm or a pilot farm exists, there must be adequate separation for each environment.
- If the agency supports more than one virtual environment, each virtual environment must be independent from each other to prevent single point of failure.
- The Virtual Desktop Tier must be protected in a logical enclave so that VDI resources are protected and segregated from other enterprise IT resources.
- Devices that have access to FTI must be further segregated into a logical enclave to provide the most granular protection for FTI.
- External facing Access Tier components such as web servers and interface servers must be placed behind filtering devices in a Demilitarized Zone (DMZ).
Access Control
All devices must be evaluated for compliance prior to attempting connection to the VDI. This technical guidance does not “compare the features or security options offered by different products, nor does it provide an opinion of one product over another". The agency should ensure that following access controls are implemented in the VDI:
- Access to each resource must be granted explicitly to prevent unauthorized access,
- Anonymous and public access must be disabled,
- Administrative and monitoring traffic must originate from authorized IP address ranges,
- Administrative consoles must be restricted to authorized personnel only and
- Network Access Control (NAC) or device authentication must be implemented to ensure only authorized clients are permitted to access the virtual desktop environment.
Securely configure Virtual Desktop and Access Tier Components
The virtual desktop environment must be securely configured, patched for security vulnerabilities and supported by the vendor. The underlying Operating System (OS) must also be securely configured as required by the IRS Office of Safeguards via published Safeguard Computer Security Evaluation Matrices (SCSEM).
Several configuration changes may be needed to become compliant:
- Installation of anti-virus software on all platforms supporting the virtual environment.
- Repositioning an existing firewall or adding additional boundary protection to adequately protect internal resources.
- Changing default ports of the web server and removing any sample sites installed by the web server for web interfaces used by the virtual environment.
- Encrypting all web interfaces using HTTPS to ensure the confidentiality and integrity of web traffic, ensuring that TLS certificates are current and confirm all encryption mechanisms are compliant with the latest version of FIPS 140.
Managing user privileges
While it is important to manage user privileges in a traditional client-server environment, it is equally important to limit the permissions of virtual desktop administrators and permissions given to end users on their virtual desktop by:
- Implementing Role-Based Access Control (RBAC) to effectively manage user privileges.
- System administrators should not be able to authenticate directly as root and must use “sudo” credentials.
- Restrict users from installing software in the virtual environment to prevent use of unauthorized and malicious software.
- Only allow end users to have permissions for daily business operations unless a business justification is documented and approved by management.
- Restricting configuration files, log files and automated scripts placed on the virtual machine to virtual desktop administrators only.
- Prevent unauthorized access from end users with an authorized access control list.
- Protecting virtual machine files, snapshots and roll back files from unauthorized access. These files can recreate the user session and sensitive information can be disclosed.
Limit functionality provided by the virtual desktop
FTI must be protected and remain under agency control at all times. There are a number of common parameters and options that enhance security of the virtual desktop, some of which also prevent users from transferring FTI to their Client Tier devices:
- Copy and clipboard functions such as the “Client clipboard redirection” must be disabled to prevent unauthorized access and disclosure of FTI.
- Disable client drive mapping to prevent users from storing data on their local devices or on the virtual workstation.
- File transfer to local device and USB support must be disabled to ensure FTI cannot be stored or transferred either locally or onto removable media.
- Disable shadowing to ensure sensitive data is limited to authorized users only for a virtual desktop solution that supports shadowing.
- Disable unnecessary functionality
- Capability to deliver multimedia information.
- Support of collaboration devices such as webcam and microphones.
- Disable printer configuration so that FTI cannot be printed locally.
- Configure the virtual desktop to prompt users for credentials before attempting to resume a disconnected session after network disruption.
- Remove anonymous or public user accounts from the virtual environment. Published resources must be restricted to authorized users only.
Disable snapshots and roll back functionality if they are not required. If changes to the environment are needed, then it must be approved by the agency for use. See Publication 1075 Section 4.5 Configuration Management (CM-3) Configuration Change Control for additional information.
Multi-factor authentication
In accordance with Publication 1075, Section 4.1 Access Control AC-17, Remote Access, multi-factor authentication must be implemented for remote access of FTI to ensure only authorized users have access to FTI.
Remote access and virtualization technologies allow a user to access FTI from a remote location. The threats of shoulder surfing, network sniffing and password cracking decrease the assurance level of user identity. Traditional challenge-response based authentication mechanisms are no longer sufficient to proof the identity of remote users.
Audit all privileged and administrative functions
Configure the virtual desktop environment to record all privileged and administrative functions, to include both allowed usage and denied attempts of credentials. Security events must be reviewed regularly, at least on a weekly basis, by security personnel. For a list of security events that must be recorded by the virtual environment, please reference Publication 1075, Section 4.3 Audit and Accountability, AU-2 Audit Events.
Session confidentiality and integrity
Enable strong encryption for traffic with FTI in transit, VDI management traffic and between Client Tier communications to the virtual desktop. Encryption must be FIPS 140 validated.
References
- Publication 1075, Tax Information Security Guidelines for Federal, State and Local Agencies
- NIST Special Publication 800-46, Revision 2, Guide to Enterprise Telework and Remote Access Security PDF
- VMware View Security online documentation
- Azure Virtual Desktop documentation
- Remote Desktop Services Protocols Overview

 )
or https:// means you've safely connected to the .gov website. Share sensitive information only on official, secure websites.
)
or https:// means you've safely connected to the .gov website. Share sensitive information only on official, secure websites.