Purpose
Purpose of this document is to provide guidance to federal, state and local agencies that receive, store, process or transmit federal tax information (FTI) on the requirements for the approval, acquisition, handling, protection, and disposition of live FTI used in system testing activities. This guidance further expands upon the Live Data Testing requirements provided in IRS Publication 1075, Tax Information Security Guidelines for Federal, State and Local Agencies, Section 2.E.6.4 – Live Data Testing.
The use of live FTI in test environments should generally be avoided and is not approved unless specifically authorized by the IRS Office of Safeguards. Dummy data should be used in place of live FTI wherever possible.
Background
Live Data – as defined in Internal Revenue Manual (IRM) 10.5.1.2.2 Sensitive But Unclassified (SBU) Data: Live data is production data in use. Live means that when changing the data, it changes in production. Authorized personnel may extract the data for testing, development, etc., in which case, it is no longer "live." Live data often is SBU data (including PII and tax information); however, tax information stays tax information whether it is live in a production environment or is removed to a non-production environment. The use of live data in testing environments is limited to tax administration or other authorized IRS purposes and may be disclosed only to those individuals with a need to know.
The disclosure of FTI is restricted to authorized federal, state and local agencies per the provisions of IRC Section 6103, Confidentiality and Disclosure of Returns and Return Information. As such, IRS Publication 1075 outlines the requirements and guidelines for agencies in receipt of FTI to establish procedures to ensure the adequate protection of the FTI data they receive.
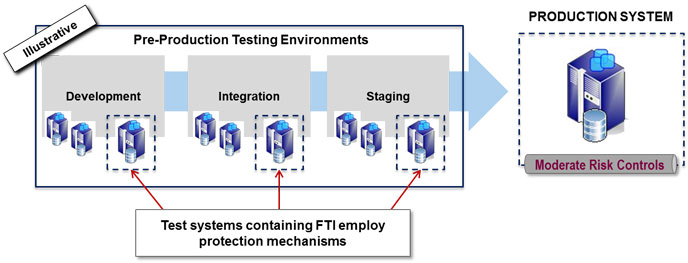
Any systems within pre-production testing environments (as illustrated in Figure 1), ideally will be configured according to Publication 1075 requirements. However, the Office of Safeguards understands most agencies may not be able to fully implement all Publication 1075 requirements in a test environment. The purpose of the Live Data Request is for agencies to explain how they will protect FTI while it resides in the test environment to provide the Office of Safeguards a level of assurance that the controls required for a production environment are implemented to the extent possible, knowing the environment won’t completely meet Publication 1075 requirements. At a minimum the controls detailed in the Protection Mechanisms section below will need to be implemented.
Figure 1 – Pre-production testing environments
Why is live data used in testing environments?
Live data in test systems allows greater accuracy for the development team to identify potential gaps in the system. For example, utilizing data that mimics live data can allow the systems development team to cover all conditions for the system changes that need to be tested as well as having other normal production data characteristics to observe near-production state results. Testing efforts that use live FTI primarily fall into two categories: one-time testing and ongoing testing.
An example of a one-time testing use of live FTI would be for system testing that is done prior to a new system implementation, and once testing has validated the data will work properly the live FTI is not required to continue to remain in the test environment. For one-time testing efforts, Safeguards requires the FTI be deleted from systems and databases upon completion of testing efforts, and that the hard drive of the test systems be cleared electronically prior to repurposing the system for other state agency testing efforts.
Duration for on-going test activities will be agreed upon as part of the live data request process. Some examples of on-going testing efforts include:
- Testing of extract, transform, load (ETL) process to validate Federal data load to a database.
- Application testing of income modelling that requires data match between the entire population of state and Federal returns, where building a set of dummy data is not feasible.
- Testing audit selection queries that run against the entire population of Federal returns to identify potential state non-filers; where building a set of dummy data that would correspond to actual state returns is not feasible.
Security risks of using live data in testing environments
System development and pre-production test environments are often not configured to the same level of security as a production system, making them a weak link in an organization’s security posture. For example, an agency may have multiple business units that share common IT infrastructure, but have unique risk profiles that require varying levels of security controls to be employed due to the unique mission of each business unit. Through the “least common denominator” concept, a potential adversary levels the playing field by compromising the business unit with the lowest level of information security controls, and then traverses the network to ultimately compromise the business unit processing the targeted sensitive and confidential information.
Applying security controls to the pre-production test environment will allow agencies to take the pre-production test environment out of the equation as the “least common denominator” for security, and proactively integrate compliance activities and security into the SDLC process, resulting not only in becoming compliant with IRS Safeguarding requirements, but also creating a “culture” of security through cost effective application of security controls.
Requesting live FTI data - process overview
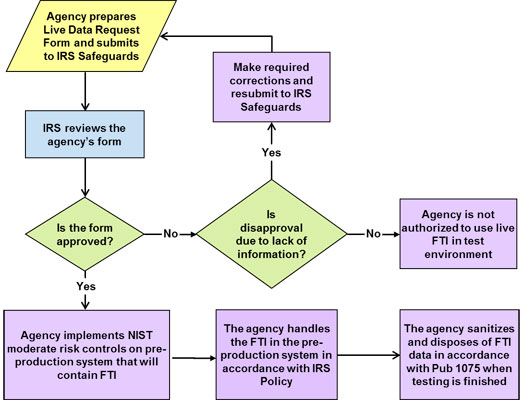
Per IRS Publication 1075, agencies must submit a request to the IRS Office of Safeguards for authority to use live data for testing, providing a detailed explanation of the safeguards in place to protect the data and the necessity for using live data during testing. The process flow in Figure 2 below provides a flow chart for the steps needed as a part of the live data request process for using live FTI in pre-production systems.
A template is provided on the IRS Office of Safeguards web site for agencies to complete and submit to the IRS. All submissions should be sent to the IRS Safeguards mailbox: SafeguardReports@irs.gov with the subject line: Live FTI Data Request.
Figure 2 – Live data request process overview
Protection mechanisms
As stated earlier, if approved by IRS, any pre-production system that receives, processes, stores or transmits FTI is required to meet all of the security requirements outlined in IRS Publication 1075. Applying security controls to the pre-production test environment will allow agencies to proactively integrate compliance activities and security into the SDLC, resulting in cost effective security and compliance with IRS Safeguarding requirements. The following is a high-level description of some of the critical control areas from the Publication 1075:
- Physical security controls: The area where the test systems are stored must meet minimum protection standards outlined in Publication 1075, which includes two barriers to access FTI under normal security.
- Logical access controls: The agency must ensure that only authorized employees or contractors (if allowed by statute) of the agency receiving the information have access to the system with FTI, and that user accounts for the test systems are managed according to production system standards for establishing, activating, changing, reviewing, disabling and removing accounts.
- Identification and authentication: The test system must be configured to uniquely identify users, devices and processes via the assignment of unique user accounts and authentication methods such as passwords, tokens, smart cards, etc.
- Audit and accountability: The test system must generate a level of audit records to the extent necessary to capture unauthorized access of FTI by unique users. As part of system testing, the agency should try to mimic the audit capabilities that will be in place in production to ensure auditing functions properly.
- Labeling: If FTI is commingled with other state data, the FTI must be labeled at the data element level to identify it as FTI at all times. This includes data that may be commingled within a database or data warehouse.
- Encryption: All FTI in transit must be encrypted when moving across a Wide Area Network (WAN) and within the agency’s Local Area Network (LAN).
- Incident response and reporting: The agency must follow the incident response and reporting procedure used for production systems for any incident involving FTI that occurs on a test system. This includes notification to the Office of Safeguards no later than 24 hours after the identification of a possible incident. System testers are trained and aware of the incident response process.
- Contractor access: Agencies must follow the regulations in the statute for disclosing FTI to a contractor. For agencies that utilize a contractor for system testing activities, the Safeguarding language must be included in their contract, and the agency must provide notification to the IRS 45 days prior to the contractor having access to FTI, and the contractor has been trained on both disclosure awareness and incident response.
- Limited timeframe: IRS approval for on-going testing is valid for three years from the date of the approval. If the agency needs to continue the use of FTI in pre-production testing activities past the three-year timeframe, a new request for live data must be submitted to the IRS.
- Reporting: The agency must notify the IRS a minimum of 45 days prior to moving FTI to the pre-production environment and update their SSR section 9.4.6. If the annual SSR has already been submitted the agency must report the testing the following year. Additionally, for approved on-going testing efforts the agency must report any changes to their pre-production environment or uses of the FTI in the pre-production environment that was not previously covered in the request for live data with a new submission.
- Sanitization and disposal: Agencies must follow data sanitization and disposal procedures in accordance with Publication 1075 once the FTI is no longer needed in the test environment. For one-time testing efforts agencies must delete the data from the test system, and clear the system’s hard drive prior to repurposing the system for other state agency testing efforts. For on-going testing efforts, the FTI may remain on the system for the duration of the approved testing timeframe, however once the approved testing timeframe expires, the agency must delete the data from the test system, and clear the system’s hard drive prior to repurposing the system for other state agency testing efforts; or submit a new request for live data testing to the IRS.
Please submit requests for the use of live data testing on the Live data testing notification form DOCX.
Resources
- Publication 1075, Tax Information Security Guidelines For Federal, State and Local Agencies
- NIST SP 800-53 Revision 5, Recommended Security Controls for Federal Information Systems and Organizations PDF
- 10.5.1.2.2 Sensitive But Unclassified (SBU) Data

 )
or https:// means you've safely connected to the .gov website. Share sensitive information only on official, secure websites.
)
or https:// means you've safely connected to the .gov website. Share sensitive information only on official, secure websites.