On this page
- Introduction
- Cloud computing definition
- Service and deployment models
- Third-party partnerships
- Security responsibility
- What the Office of Safeguards considers a cloud
- What the Office of Safeguards does not consider a cloud
- Mandatory requirements for FTI in a cloud environment
- Frequently asked questions
- Resources
Introduction
In June 2012, the federal government launched the Federal Risk and Authorization Management Program (FedRAMP) to explain the unique security requirements surrounding cloud computing. FedRAMP is a subset of the National Institute of Standards and Technology’s (NIST) Special Publication (SP) 800-53 security controls targeted towards Cloud Service Provider (CSP) and customer security requirements.
Based on NIST guidance, FedRAMP baseline, industry best practices and the IRS Publication 1075, the IRS Office of Safeguards (Safeguards) provides this guidance to agencies for securing federal tax information (FTI) in a cloud environment. This guidance is subject to change. Agencies and their CSPs should also review the requirements of FedRAMP and confirm overall compliance with these guidelines.
As agencies look to reduce costs and improve reliability of business operations, cloud computing offers an alternative to traditional data center models. Cloud solutions reduce direct hardware expenditures and may eliminate redundant operations and consolidate resources.
While cloud computing offers many benefits, it is not without risk. The agency is still responsible for monitoring and addressing security issues that arise with FTI in a cloud environment. The primary security concerns are:
- Data from multiple customers could commingle in the cloud environment
- Data is not stored in an agency-managed data center
- Data is not transferred securely between the CSP and service consumer
- Programs that access FTI in a cloud environment including authentication and authorization controls may not be secured per customer requirements
- The agency must rely on the provider’s security controls for protection
Limiting access to authorized individuals becomes a much greater challenge with the increased availability of data in the cloud. Agencies may have greater difficulties to identify FTI when segregated or commingled in the cloud environment.
Agencies that use a public cloud model must have increased oversight and governance over the security controls implemented by their CSP. Monitoring and addressing security issues that arise with FTI in a cloud environment remain the responsibility of the agency.
Cloud computing definition
As defined by NIST SP 800-145, “Cloud computing is a model for enabling ubiquitous, convenient, on-demand network access to a shared pool of configurable computing resources (e.g., networks, servers, storage, applications, and services) that can be rapidly provisioned and released with minimal management effort or service provider interaction. This cloud model is composed of five essential characteristics, three service models, and four deployment models.”
Essential characteristics
- On-demand self-service. A consumer can unilaterally provision computing capabilities, such as server time and network storage, as needed automatically without requiring human interaction with each service provider.
- Broad network access. Capabilities are available over the network and accessed through standard mechanisms that promote use by heterogeneous thin or thick client platforms (e.g., mobile phones, tablets, laptops, and workstations).
- Resource pooling. The provider’s computing resources are pooled to serve multiple consumers using a multi-tenant model, with different physical and virtual resources dynamically assigned and reassigned according to consumer demand. There is a sense of location independence in that the customer generally has no control or knowledge over the exact location of the provided resources but may be able to specify location at a higher level of abstraction (e.g., country, state, or datacenter). Examples of resources include storage, processing, memory, and network bandwidth.
- Rapid elasticity. Capabilities can be elastically provisioned and released, in some cases automatically, to scale rapidly outward and inward commensurate with demand. To the consumer, the capabilities available for provisioning often appear to be unlimited and can be appropriated in any quantity at any time.
- Measured service. Cloud systems automatically control and optimize resource use by leveraging a metering capability at some level of abstraction appropriate to the type of service (e.g., storage, processing, bandwidth, and active user accounts). Resource usage can be monitored, controlled, and reported, providing transparency for both the provider and consumer of the utilized service.
Service and deployment models
An agency’s cloud implementation is a combination of a service model and a deployment model.
Service models
The resource stack provided as part of the cloud solution and the responsibilities which fall between the agency and the CSP define service models. NIST SP 800-145 outlines the possible service models that may be employed during a cloud implementation. Many Cloud Service Offerings (CSO) will include options spanning each of these service models.
- Software as a service (SaaS). The capability provided to the consumer is to use the provider’s applications running on a cloud infrastructure. The applications are accessible from various client devices through either a thin client interface, such as a web browser (e.g., web-based email), or a program interface. The consumer does not manage or control the underlying cloud infrastructure including network, servers, operating systems, storage, or even individual application capabilities, with the possible exception of limited user-specific application configuration settings.
- Platform as a service (PaaS). The capability provided to the consumer is to deploy onto the cloud infrastructure consumer-created or acquired applications created using programming languages, libraries, services, and tools supported by the provider. The consumer does not manage or control the underlying cloud infrastructure including network, servers, operating systems, or storage, but has control over the deployed applications and possibly configuration settings for the application-hosting environment.
- Infrastructure as a service (IaaS). The capability provided to the consumer is to provision processing, storage, networks, and other fundamental computing resources where the consumer is able to deploy and run arbitrary software, which can include operating systems and applications. The consumer does not manage or control the underlying cloud infrastructure but has control over operating systems, storage, and deployed applications; and possibly limited control of select networking components (e.g., host firewalls).
Deployment models
- Private cloud. The cloud infrastructure is provisioned for exclusive use by a single organization comprising multiple consumers (e.g., business units). It may be owned, managed, and operated by the organization, a third party, or some combination of them, and it may exist on or off premises.
- Community cloud. The cloud infrastructure is provisioned for exclusive use by a specific community of consumers from organizations that have shared concerns (e.g., mission, security requirements, policy, and compliance considerations). It may be owned, managed, and operated by one or more of the organizations in the community, a third party, or some combination of them, and it may exist on or off premises.
- Public cloud. The cloud infrastructure is provisioned for open use by the general public. It may be owned, managed, and operated by a business, academic, or government organization, or some combination of them. It exists on the premises of the cloud provider.
- Hybrid cloud. The cloud infrastructure is a composition of two or more distinct cloud infrastructures (private, community, or public) that remain unique entities, but are bound together by standardized or proprietary technology that enables data and application portability (e.g., cloud bursting for load balancing between clouds).
Table 1: Cloud deployment models
| Model | System management | System owners | System location |
|---|---|---|---|
| Public | Provider | Provider | Provider site |
| Private | Agency or provider | Agency or provider | Agency or provider site |
| Community | Agency or provider | Agency or provider | Agency or provider site |
| Hybrid | Agency or provider | Agency or provider | Agency or provider site |
The risk to data varies in each of the four deployment models, with private cloud typically being the lowest risk model, and public cloud being the highest risk model. Depending on the deployment model, compensating controls can be accepted in place of the mandatory requirements provided those compensating controls provide the same level of protection as mandatory controls for safeguarding FTI.
Third-party partnerships
These are the two types of partnerships that agencies can have with third parties:
Independent software vendors (ISV) - ISVs often develop a specific application (app) or software on top of a CSO, the CSO must be FedRAMP authorized but the agency is responsible for implementation of security controls for the app or software. Safeguards will assess this during reviews.
System integrators (SI) - SIs provide customized services including custom development, test, operations, and maintenance. SIs build custom systems to meet the customer’s needs. If using CSOs, the CSOs must be FedRAMP authorized. The security control implementation of the SI-built system is the responsibility of the agency and is included in the Safeguards review process.
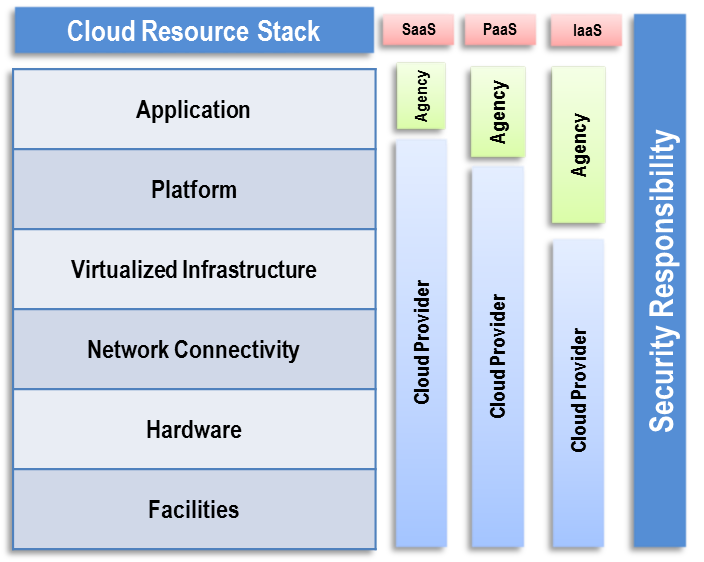
Security responsibility
The service and deployment model used in a cloud computing environment determines the responsibility for security controls implementation between the agency and the CSP for protection of FTI that is stored or processed in cloud environments. The security control responsibility is heavily dependent on the service and deployment models of the solution the agency adopts. For example, if the solution is a SaaS email solution, the agency may be responsible for a small subset of security control responsibilities including access controls. If the agency is deploying their own applications to a PaaS or IaaS solution, they will have greater responsibility for securing the application layer, and potentially the platform and middleware. They may also have responsibilities in almost all the Publication 1075 (NIST 800-53) control families except for possibly the personnel and physical security requirements. Figure 1 is an illustration of the differences in scope between the cloud consumer (agency) and CSP for each of the service models. Many CSOs can provide a mix of services that span each of the security responsibilities (e.g., an environment with IaaS storage services and PaaS database services). Some security controls may be shared between the CSP and agency (e.g., CSO provides the ability to use Federal Information Processing Standards (FIPS) compliant encryption, but the agency must configure it).
Figure 1. Security control responsibility
Figure 1 is a notional illustration of the differences in scope between the cloud consumer (agency) and cloud provider for each of the service models discussed above.
What the Office of Safeguards considers a cloud
The above definitions apply to the industry at large. Below are examples of what the Office of Safeguards considers a cloud environment. For these, Safeguards would require a 45-day notification and perform a review which will assess the solution using the Safeguards Computer Security Evaluation Matrix (SCSEM).
- Traditional CSOs: An agency contracts with a well-known CSP for supporting and implementing FTI systems. For example only:
- Amazon Web Services
- Google Workspace, Google Services
- Microsoft 365, Microsoft Azure
- Data storage solutions: An agency uses third-party provided data storage and movement systems which meet cloud definition (multi-tenant, multiple facilities, etc.). For example only:
- Box.com
- Dropbox.com
- Kiteworks.com
Note: No one particular technology over another is endorsed by the Office of Safeguards, agencies must determine Cloud solutions based on need.
What the Office of Safeguards does not consider a cloud
Examples of what Safeguards would not consider a cloud environment. These would not require a 45-day notification or use of the cloud computing SCSEM during a Safeguards review:
- Contracted third-party services: An agency contracts a specific business process which a third-party implements using their own technology. Examples:
- Collection agencies
- Call centers
- Field offices
- Hosted solutions/Systems: An agency maintains the ownership and configuration of technologies located in a third-party managed facility:
- Agency only relies on the third-party for rack space, power, and cooling
- Agency maintains root-level controls of its technologies
- Contractor-managed consolidated data centers: A state outsources the management of a consolidated data center (CDC) to a third-party contractor.
- Safeguards still must assess these data centers with existing methodologies
- Contractors may have access issues to certain data types
- Agency-managed virtual environments: An agency or state has a virtual environment which hosts FTI systems. The virtual environment is on-site or at a CDC.
- Assessment can be performed using the appropriate virtualization SCSEM
- Agency may use the word “cloud” to describe their own systems but will not be assessed as such
Mandatory requirements for FTI in a cloud environment
The following mandatory controls apply to all cloud service and deployment models. However, as stated earlier, depending on the deployment model, compensating controls can be accepted in place of the mandatory requirements, but they must give the same level of protection as mandatory controls for safeguarding FTI. The Office of Safeguards will evaluate potential compensating controls as part of the cloud computing notification (see requirement).
To use a cloud computing model to receive, transmit, store or process FTI, the agency must follow all Publication 1075 requirements. The following mandatory requirements from Section 3.3.1 apply for storing FTI in a cloud environment.
Agencies maintaining FTI within cloud environments must use a CSO that is FedRAMP authorized for medium impact information systems.
Cloud solutions used to receive, process or store FTI must undergo a complete assessment using the FedRAMP authorization framework from an authorized third-party assessment organization (3PAO). The 3PAO assessment ensures that the CSO functions as intended and that proper security controls are addressed. The assessment must result in an Authority to Operate (ATO) granted by a federal agency or a provisional Authority to Operate from the FedRAMP Joint Advisory Board (JAB). Only FedRAMP-authorized CSOs may receive, process, store or transmit FTI. The discovery of FTI in a non-FedRAMP cloud during a Safeguards review will result in a critical finding. A higher-level CSO (e.g., SaaS) without specific FedRAMP authorization built on top of a lower-level (e.g., IaaS) FedRAMP authorized CSO still requires FedRAMP authorization.
Note: Safeguards will rely on the 3PAO assessment and FedRAMP ATO requirements for the CSO instead of conducting regular Safeguards reviews for CSPs. FedRAMP authorization alone, nor 3PAO attestations, will not meet IRS Publication 1075 requirements for cloud computing.
Agencies must use CSPs and CSOs where:
- All FTI physically resides onshore: in systems located within the United States legal jurisdiction (e.g., U.S. states, District of Columbia, U.S. territories, U.S. embassies, U.S. military bases); and
- All access and support of the agency’s system with such data is performed from the U.S.
FTI and controls protecting its confidentiality may not be accessed by personnel located outside of the US’s legal jurisdiction: offshore. All physical locations where FTI is stored, transmitted, processed and/or received must remain onshore. This includes all primary and secondary data centers and any backup facilities. Agency information systems with FTI in cloud environments may not be accessed by CSP administrators from offshore networks. This also applies to any systems components including storage, virtualized systems, operating systems, and networking. FTI may not be received, stored, processed, or disposed via information systems located offshore. The discovery of offshore storage and/or access to FTI during a Safeguards review will result in a critical finding.
Agencies and/or their CSPs must provide the Office of Safeguards a complete listing of all data centers within the cloud environment where FTI will be received, processed, transmitted, or stored.
In addition to certifying that all data centers, environments, and equipment reside onshore, the agency and provider must disclose all physical locations where FTI is received, processed, stored, and maintained. Safeguards cannot accept the implementation of cloud solutions without a full understanding of the physical locations where FTI is processed, in addition to understanding the logical protections the CSP solution provides.
Note: Safeguards will rely on the 3PAO assessment and FedRAMP ATO requirements for the CSO instead of doing regular Safeguards reviews for CSPs.
To use a cloud environment that receives, processes, stores, or transmits FTI, the agency must submit a Cloud Computing Notification to the Safeguards containing the following information at least 45 days prior to transmitting FTI into a cloud environment to safeguardreports@irs.gov.
Publication 1075 Section 2.E.6.1, Cloud Computing Environments requires agencies to:
- Document all agency-managed security and privacy controls
- Document the cloud service provider's FedRAMP authorization such that the Office of Safeguards does not have the responsibility to assess the physical security of cloud service provider facilities
- Document the physical locations where FTI will be processed to ensure FTI remains onshore
- Explain how encryption will be used to prevent unauthorized disclosures to cloud service provider employees
The IRS strongly recommends that any agency planning on using a cloud computing model contact the Office of Safeguards at safeguardreports@irs.gov to schedule a conference call to discuss the details of the planned cloud computing implementation and to request a copy of the FTI Cloud Notification Form.
Software, data, and all services that receive, transmit, process or store FTI must be isolated within the cloud environment so that other cloud customers sharing physical or virtual space cannot access other customer data or applications.
One of the most common compliance issues with FTI is data location. Use of an agency-owned computing center allows the agency to structure its computing environment and to know in detail where FTI is stored and what safeguards are used to protect the data.
In contrast, many cloud computing services don’t disclose to the agency detailed information about the location of their data. This makes it difficult to know if sufficient safeguards are in place to meet legal and regulatory compliance requirements.
IRS Publication 1075, Section 2.C.5, Commingling of FTI, recommends separating FTI from other information to the maximum extent possible. Organizing data in this way will reduce the chance of unauthorized data access and disclosure.
If complete separation is not possible, the agency must label FTI down to the data element level. Labeling must occur prior to introducing the data to the cloud and the data must be tracked accordingly through audit trails captured for operating systems, databases and applications that receive, store, process or transmit FTI.
IRS Publication 1075, Section 4.3, Audit and Accountability, states audit logs must enable tracking activities to take place on the system. It also contains requirements for creating audit-related processes at both the application and system levels. Within the application, auditing must be enabled to the extent necessary to capture access, modification, deletion, and movement of FTI by each unique user. This requirement also applies to data tables and databases inside or outside of the application. Agencies must coordinate the access and protection of audit information with its CSPs.
IRS Publication 1075, Section 3.3.1.G, requires that the agency must use a legally binding contract, Service Level Agreements (SLA), with their CSP to establish security policies and procedures for how FTI is stored, handled, and accessed inside the cloud.
While the agency may not always have direct control over FTI, they still have responsibility for protecting it while in the cloud. The agency’s ownership rights over the data must be firmly established in the service contract to enable a basis for trust. The SLA helps mitigate the security risks that comes with the agency’s lack of visibility and control in a cloud environment. Importantly, agencies should establish SLAs with CSPs that clearly identify Publication 1075 security control requirements. The SLAs must clearly show who has responsibility between the provider and customer to implement those requirements. At a minimum, SLAs with CSPs must include:
- Contract language - per IRS Publication 1075, Exhibit 7,
- Cybersecurity - CSP must meet all requirements per IRS Publication 1075, Section 4, NIST 800-53 Security and Privacy Controls,
- CSP personnel - FTI access requirements include:
- Annual training
- Background check
- Justifiable need
- Incident response - CSPs must follow all requirements per IRS Publication 1075, Section 1.8, Reporting Improper Inspections or Disclosures. The CSP and agency must report incident information within 24 hours of an unauthorized disclosure or data breach to IRS Office of Safeguards.
- Agreement on the scope of security boundary - section of the cloud where FTI is accessible and systems where FTI resides. The agency must ensure the SLA includes boundary details.
- Clearly states agency’s right to require changes – changes to their section of the cloud environment and that CSPs will comply with IT policies and procedures provided by the agency
- The notification requirement - notifying the agency prior to executing any agreement to disclose FTI or at least 45 days prior to the disclosure of FTI to a CSP’s contractor. This requirement allows the agency to include appropriate contractual language and hold contractors to safeguarding requirements, per IRS Publication 1075, Exhibit 6, Contractor 45-day Notification Procedures
- CSP employee awareness and training - requirements for access to FTI and incident response. IRS Publication 1075, Section 2.D.2, Training Requirements, states employees must be certified and maintain annual certification in the agency’s security policy and procedures to access FTI. The agency should track CSP employee training, the Office of Safeguards will inspect the agency’s compliance during reviews.
Data must be encrypted when in the cloud, NIST’s SP 800-144 states, “Data must be secured while at rest, in transit and in use, and access to the data must be controlled.”
- In transit – The agency must ensure FTI is encrypted in transit within the cloud environment. All mechanisms used to encrypt FTI must be Federal Information Protection Standards (FIPS) 140 validated and operate using the FIPS 140 validated module. IRS Publication 1075 Section 4.18, Transmission Confidentiality, and Integrity (SC-8) requires encryption of FTI in transit.
- At rest – The agency must ensure FTI is encrypted while at rest in the cloud using a NIST-validated, FIPS 140 validated encryption module(s). Encryption protects the confidentiality and integrity of the data and provides a methodology for segmenting an agency’s data from others while stored. In a cloud environment, protection of data and data isolation are a primary concern. Encryption of data at rest assures the agency that FTI is properly protected in the cloud.
The Office of Safeguards does not advocate specific mechanisms to accomplish encryption as long as they are FIPS 140 validated and configured securely. To prevent CSP access (contractor access) to FTI, agencies must retain control of the encryption keys used to encrypt and decrypt the FTI and be able to provide information about who has access to these keys.
Agencies must satisfy this requirement, effectively preventing logical access to the data from the CSP, to use CSOs in a public cloud deployment model, and for cloud infrastructure for data types that have contractor-access restrictions. This is often accomplished by configuring key management solutions (KMS) to use customer managed (encryption) keys (CMK), on a FIPS 140 compliant hardware security module.
Storage devices that housed FTI must be securely sanitized and/or destroyed using methods provided in NIST SP 800-88, Guidelines for Media Sanitization.
If a storage device fails, or when the data is moved within or removed from a cloud environment, CSPs must take actions to ensure residual FTI is no longer accessible. The destruction or sanitization methods apply to both individual devices and when the agency removes data from a cloud environment or moves it to another.
The technique for clearing, purging, and destroying media depends on the type of media. Acceptable physical destruction methods include disintegration, incineration, pulverizing, shredding, or melting. CSPs must ensure repurposed media is purged to remove any residual FTI.
CSPs should consult their data storage provider to determine the best method to sanitize the storage device. If the storage device will no longer be in service, CSPs must ensure the residual data is purged.
The agency must conduct an annual assessment of all security controls on information systems in a cloud environment used for receiving, processing, storing, and transmitting FTI. This control assessment helps determine if the controls are implemented correctly, operating as intended, and keeps risk at an acceptable level. FEDRAMP and 3PAO certifications of the cloud environment do not replace the need for this risk assessment.
The agency must conduct a risk assessment or update an existing risk assessment, if one exists, when migrating FTI to a cloud environment since it is a significant change which will affect the security and privacy of their system. The agency’s risk assessment must evaluate all associated risks with implementation or migration to this new cloud environment.
The agency must review the risk assessment annually to account for any changes to the cloud environment.
Note: The Office of Safeguards will evaluate this risk assessment as part of the 45-day notification requirement and agency inspections.
Cloud implementations represents a logical segmented system within the larger CSPs environment which is accessed remotely over the public internet. Since remote access is needed to interact with this logical system, multi-factor authentication (MFA) is required.
MFA requires at least two of three criteria:
- Something a user knows:
- Password
- Personal identification number (PIN)
- Something a user has:
- Hardware cryptographic token
- Common access card (CAC)
- Something a user is (biometric):
- Fingerprint scan
- Iris scan
The requirement to use MFA includes access to CSO management consoles, access to system components, and remote administration of a server. NIST SP 800-63B, Authentication and Lifecycle Management, provides guidance for implementing MFA. Safeguards requires Authenticator Assurance Level (AAL) 2 for MFA.
The CSP must identify, document, and implement customer (agency) defined security controls. The customer defined security controls, as implemented, must comply with Publication 1075 requirements.
CSPs may designate selected controls as customer defined. For customer defined security controls, the agency must identify, document, and implement the customer defined controls, per Publication 1075. The agency may need to partner with the CSP to implement some controls, but the agency keeps the primary responsibility.
The agency’s capability to test the functionality and security control implementation of a subsystem within a cloud environment is more limited than the ability to perform testing within the agency’s own infrastructure. The agency can use other mechanisms such as third-party assessments to establish trust with the CSP.
Safeguards will test agency-managed security controls during reviews using the appropriate SCSEM for applications, operating systems, database management systems, etc. Safeguards will determine the necessary requirements based on the cloud service model (i.e., PaaS, IaaS, SaaS) used to process FTI and will discuss with the agency during the 45-day notification process or prior to a review. The Safeguards review team will leverage the Cloud Computing SCSEM to assess additional controls for the CSO. Safeguards will also rely on the 3PAO assessment and FedRAMP ATO requirements for the CSO instead of doing regular Safeguards reviews for CSPs.
Note: The IRS strongly recommends that any agency planning on using a cloud computing model contact the Office of Safeguards at safeguardreports@irs.gov to schedule a conference call to discuss the details of the planned cloud computing implementation and to request a copy of the FTI Cloud Notification Form.
Frequently asked questions
Yes, it must meet all of the mandatory Safeguards’ requirements to include FedRAMP authorization, data isolation, agency-controlled encryption keys, and onshore access.
This may be acceptable if:
- The CSO’s support team is for specific services and not supporting a specific customer, and
- The support team is prevented from accessing customer data (e.g., via customer managed/owned encryption key and FIPS validated encryption), and
- The support team cannot otherwise affect confidentiality or integrity of customer data (e.g., FTI)
Yes, if the CSO meets all of the mandatory Safeguard’s requirements and they’re not giving contractors the ability to access FTI.
ISV, SI, (etc.) solutions hosted in a CSO that meet Safeguards’ requirements do not require additional FedRAMP authorization. Agencies need to ensure that their data is adequately isolated and protected, this can be done by ensuring the following are in place:
- Dedicated single-tenant CSO accounts with logical isolation, and
- Distinct encryption keys, and
- Access control policies
Such solution providers will be incorporated into our Safeguards review process similar to how we look at the control implementation for non-cloud contractors.
Yes, in some circumstances. Acceptance depends on the implementation of the managed services, considerations will include:
- Is the solution FedRAMP authorized for moderate impact systems?
- Does the implementation facilitate access to FTI?
Yes, if the implementation has been FIPS 140 validated and they’re not accessible by the CSP (or other contractors).
Yes, Publication 1075 Exhibit 7 must be included in contracts and subcontracts for cloud services. 3PAO attestation letters, and FedRAMP authorization does not negate this requirement. It outlines additional requirements for the CSP, to include maintaining a list of employees with FTI access and background check and FTI training requirements beyond those required under FedRAMP. Exhibit 7 also enables the agency and IRS to inspect CSP datacenters hosting/supporting the CSO, if needed:
The IRS and the Agency, with 24-hour notice, shall have the right to send its inspectors into the offices and plants of the contractor to inspect facilities and operations performing any work with FTI under this contract for compliance with requirements defined in IRS Publication 1075. The IRS’ right of inspection shall include the use of manual and/or automated scanning tools to perform compliance and vulnerability assessments of information technology (IT) assets that access, store, process or transmit FTI. Based on the inspection, corrective actions may be required in cases where the contractor is found to be noncompliant with FTI safeguard requirements.
These additional requirements would not be covered under a 3PAO attestation or a FedRAMP (P-)ATO. It is also important to ensure the language exists in a legally binding agreement with the CSP, not just the resellers.
No, agencies do not need to conduct reviews/assessments of their CSPs. The FedRAMP program requires continuous monitoring and 3PAO assessments for CSOs to maintain their (P-)ATO. However, agencies should conduct their own internal assessments of the security controls they’re responsible for in the cloud environment.
For Safeguards, a cloud product must meet all of these requirements:
- Be managed by a third party, and
- That third party only provides IT/cloud support, and
- The FTI/system will be located in a multi-tenant production facility, and
- The data/system is hosted on shared hardware, and
- The service can be categorized as IaaS, PaaS, or SaaS, and
- The system can automatically provision (or deprovision) resources based on need, and
- Customers pay for services based on usage.
Safeguards has published a decision tree PDF to help agencies determine if a service or product is considered a cloud service. Submitting the 45-day cloud notification form will help Safeguards make an official determination.
Resources
Additional information can be obtained through the following resources:
- Publication 1075, Tax Information Security Guidelines for Federal, State, and Local Agencies Safeguards for Protecting Federal Tax Returns and Return Information
- Do we have a cloud? PDF
- Federal Risk and Authorization Management Program (FedRAMP)
- NIST SP 800-125, Guide to Security for Full Virtualization Technologies
- SP 800-145, The NIST Definition of Cloud Computing
- SP 800-146, Cloud Computing Synopsis and Recommendations
- SP 800-144, Guidelines on Security and Privacy in Public Cloud Computing
- CSA Security Guidance for Critical Areas of Focus in Cloud Computing
- NIST SP 800-63, Digital Identity Guidelines – Authentication and Lifecycle Management
- NIST SP 800-88 Rev. 1, Guidelines for Media Sanitization
- NIST Cryptographic Module Validation Program

 )
or https:// means you've safely connected to the .gov website. Share sensitive information only on official, secure websites.
)
or https:// means you've safely connected to the .gov website. Share sensitive information only on official, secure websites.